Reverse-Proxy (old version)
| IP: | 192.168.88.3 |
|---|---|
| MAC: | 56:59:71:B1:85:BC |
| OS: | Debian Bullseye |
|---|---|
| Files: | configuration.yml users_database.yml authelia_portal.conf protected_endpoint.conf UpdateAuthelia.sh |
| RAM: | 1024MB |
| Cores: | 1 |
| Privileged: | No |
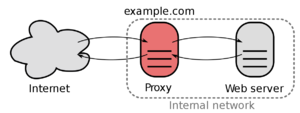
The ReverseProxy is reachable under 192.168.88.3 which is located in the ServerVLAN.
Every incoming packages from outside are forwarded to this IP.
The ReverseProxy also forces outside connections to use HTTPS/SSL and will provide a SSL-Certificate.
Basic Setup
Nginx Proxy Manager
Download installation script and run it
wget --no-cache -qO - https://raw.githubusercontent.com/ej52/proxmox/main/lxc/nginx-proxy-manager/setup.sh | sh
After installation, the webinterface should be reachable, standard login is
Email: admin@example.com
Password: changeme
Update
Update NPM with following command
wget --no-cache -qO - https://raw.githubusercontent.com/ej52/proxmox/main/lxc/nginx-proxy-manager/setup.sh | sh
Authelia
For security reasons and convenience, the login portal Authelia will be installed.
Redis-Server
Install Redis with the following command:
apt install redis-server
After installing Redis, start redis service and enable it to start after system reboot with the following command:
systemctl start redis-server
systemctl enable redis-server
Verify the status of the redis server:
systemctl status redis-server
By default, Redis listening on the localhost on port 6379. You can check it with the following command:
ps -ef | grep redis
Open Redis Config and set passphrase for redis server, which is needed in the authelia configuration file. Find # requirepass in line 507 and change it requirepass "my_redis_password"
nano /etc/redis/redis.conf
Restart redis to apply config
systemctl restart redis
Test if passphrase is working correctly and exit
redis-cli
AUTH yourpassword
exit
Installation
Download and untar latest Authelia archive:
cd ~
wget https://github.com/authelia/authelia/releases/download/v4.29.4/authelia-v4.29.4-linux-amd64.tar.gz
tar -zxvf authelia-v4.29.4-linux-amd64.tar.gz
rm authelia-v4.29.4-linux-amd64.tar.gz
Create authelia folder
mkdir /etc/authelia
Move files
mv authelia-linux-amd64 /usr/bin/authelia
mv config.template.yml /etc/authelia/config.template.yml
mv authelia.service /etc/systemd/system/
Set permissions
chmod 775 /usr/bin/authelia
chown root:root /usr/bin/authelia
configuration.yml
Create configuration file, modify and paste configuration.yml
nano /etc/authelia/configuration.yml
Restrict permissions for the configuration file
chmod 0600 /etc/authelia/configuration.yml
users_database.yml
Create users_database, modify and paste users_database.yml
nano /etc/authelia/users_database.yml
Password hash can be generated with following command
/usr/bin/authelia hash-password 'yourpassword' -i1 -k32 -l16 -m256 -p8
Restrict permissions for the users_database
chmod 0600 /etc/authelia/users_database.yml
Start authelia and check status
systemctl start authelia
systemctl status authelia
Enable authelia at boot
systemctl enable authelia
Update
To update authelia, I made an bash script: UpdateAuthelia.sh
Configure Nginx Proxy Manager
Create Proxy-Host for Authelia:
- auth.flowerhouse.at -> Scheme: http, Forward IP: 192.168.88.3, Port: 9091
- Chache Assests: On, Block Common Exploits: On
- At the advanced tab add content of file authelia_portal.conf
To enable the login portal for a host, go to the advanced tab and add the contenct of protected_endpoint.conf
- Line 3, 33 and 34 needs to be edited
Sources
- Nginx Proxy Manager (ReverseProxy)
- Nginx Proxy Manager Install Script
- Authelia GitHub (Login-Portal)
- Set up Authelia with Nginx Proxy Manager