Reverse-Proxy (old version)
| IP: | 192.168.88.3 |
|---|---|
| MAC: | 56:59:71:B1:85:BC |
| OS: | Debian Buster |
|---|---|
| Files: | reverse-proxy.conf |
| RAM: | 1024MB |
| Cores: | 1 |
| Privileged: | No |
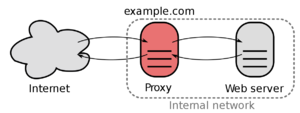
The ReverseProxy is reachable under 192.168.88.3 which is located in the ServerVLAN.
Every incoming packages from outside are forwarded to this IP.
The ReverseProxy also forces outside connections to use HTTPS/SSL and will provide a SSL-Certificate.
Basic Setup
Nginx Proxy Manager
Download installation script and run it
cd ~
wget https://raw.githubusercontent.com/Tropaion/proxmox-scripts/main/lxc/nginx-proxy-manager/setup.sh
./setup.sh
After installation, the webinterface should be reachable, standard login is
Email: admin@example.com
Password: changeme
Authelia
For security reasons and convenience, the login portal Authelia will be installed.
Redis-Server
Install Redis with the following command:
apt install redis-server
After installing Redis, start redis service and enable it to start after system reboot with the following command:
systemctl start redis-server
systemctl enable redis-server
Verify the status of the redis server:
systemctl status redis-server
By default, Redis listening on the localhost on port 6379. You can check it with the following command:
ps -ef | grep redis
Open Redis CLI and set passphrase for redis server, which is needed in the authelia configuration file
redis-cli
CONFIG SET requirepass "yourpassword"
Test if passphrase is working correctly
AUTH yourpassword
SMTP-Server
Install mailutils and postfix:
apt install mailutils postfix
Test if SMTP-Server is working:
echo "This is the body of the email" | mail -s "This is the subject line" your_email_address
Installation
Download, unzip and rename latest Authelia archive:
cd /usr/bin
wget https://github.com/authelia/authelia/releases/download/v4.26.2/authelia-linux-amd64.tar.gz
tar -xzf authelia-linux-amd64.tar.gz
rm authelia-linux-amd64.tar.gz
mv ./authelia-linux-amd64 ./authelia
After unzipping, the service file authelia.service has to be moved:
mv authelia.service /etc/systemd/system/
Create folder for the authelia configuration file:
mkdir /etc/authelia
cd /etc/authelia
Move the unzipped file config.template.yml to the created folder:
mv config.template.yml /etc/authelia/
users_database.yml
Create users_database.yml in the folder /etc/authelia/:
nano users_database.yml
An user entry looks like this:
john:
displayname: "John Doe"
password: "$argon2id$v=19$m=65536,t=3,p=2$BpLnfgDsc2WD8F2q$o/vzA4myCqZZ36bUGsDY//8mKUYNZZaR0t4MFFSs+iM"
email: john.doe@authelia.com
groups:
- admins
- dev
The password is encrypted so we have to get the hash value with:
authelia hash-password 'yourpassword'
configuration.yml
Create configuration.yml at the same folder:
nano configuration.yml
Start authelia and check status:
systemctl start authelia
systemctl status authelia
LATEST STATE:
- https://www.authelia.com/docs/configuration/access-control.html
- https://www.authelia.com/docs/configuration/authentication/file.html
Sources
- Nginx Proxy Manager (ReverseProxy)
- Nginx Proxy Manager Install Script
- certbot (Certificates)
- Authelia (Login-Portal)
- Redis-Server
- DigitalOcean (SMTP-Server)